main
FIVEM CIPHER PANEL BASIC ANALYSIS AND INFECTION PAYLAOD DUMPS
In this repo you will find,
-> Infection Dumps from 15/03/2025
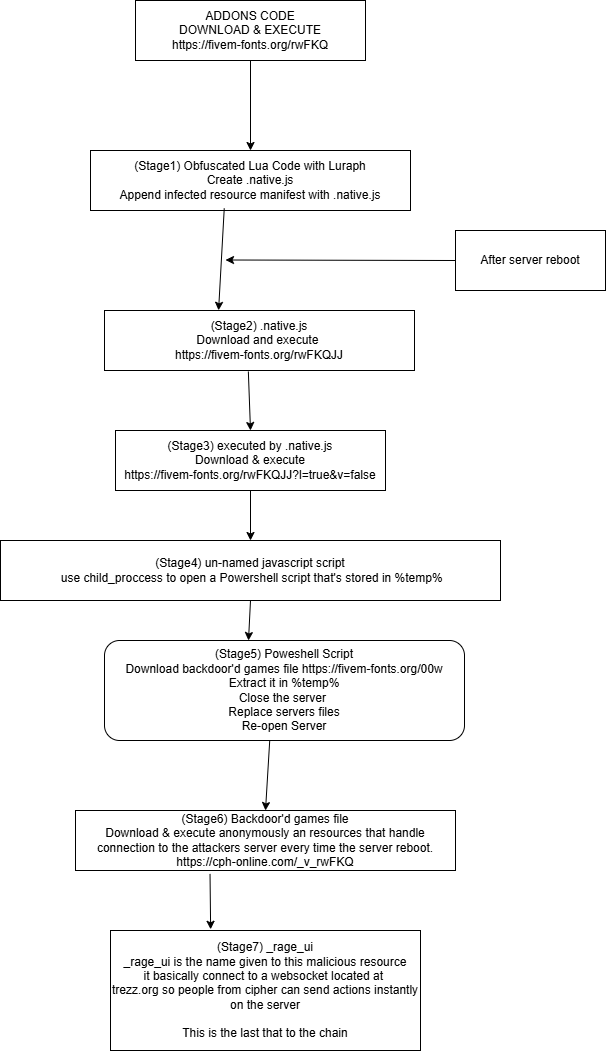
-> A schema on how it work
-> The repo doesn't contain de-obfuscated payloads.
-> What to do if i got infected ?
-> About Payoad obfuscation
-> Stage 1 : Use Luraph
-> Stage 2 : use some basic custom Xor encryption really easy to decrypt even chatgpt do it.
-> Stage 3 : Use https://obfuscator.io/ you can partially revert with https://obf-io.deobfuscate.io/ (You will have to cleanup junk code manually.)
-> Stage 4 : Some VM Like obfuscation for Javascript didn't look into it.
-> Stage 5 : Not obfusctated clear-text powershell.
-> Stage 6 : Backdoor'd DLLs and stuff didn't take the time to reverse it.
-> Stage 7 : For lua files its Luraph, For JS files its https://obfuscator.io/
-> If you got infected : Re-install completly the server OS, and do not re-use your old server-data folder. Why ? CIPHER give full OS control to the attackers and so they can execute system command remotely and install other shit on your machine. and btw avoid running FIVEM Servers as Administrator/Root.
A schema on how it works.
Description
Languages
Lua
93.7%
VBScript
6.3%